How Much Do Cyber-Threats Cost
Every day groups of experienced cybercriminals gain control over other people’s computers and gadgets by implementing series of programs that destroy particular websites. In several minutes these programs shutdown ATM stations, companies, phone lines, and even governmental websites of different countries. That is why many countries now pay more and more attention to cybersecurity and control over informational resources.
Recently one of the world leaders in informational technologies sphere, Cisco released its 10th annual report on informational security where it analyzed the latest news about threats and the current situation in the field of informational security.
Senior vice-president and executive director of the company working in informational security John Stuart claimed, “In 2017, cyber-space is a business and businesses run in cyber-space, and it requires a completely different approach and different results. One needs to be always developing and this development should be estimated regarding effectiveness, costs, and wisely thought-of risks. Report on informational security shows and, I hope, grounds our answers to problems of budget, staff, innovations, and architecture.”
Almost 3000 informational security directors and heads of IS departments from all around the world took part in the research.
According to the research more than a third of the organizations who have had their informational systems hacked in 2016 spoke about significant (more than 20%) losses of income, lost opportunities, and the outflow of customers. Most of these organizations, after such attacks, began to improve technologies which protect them from threats, started dividing functions of IT, and for the departments that provided informational security, started intensifying trainings and implementing methods for cutting the risks.
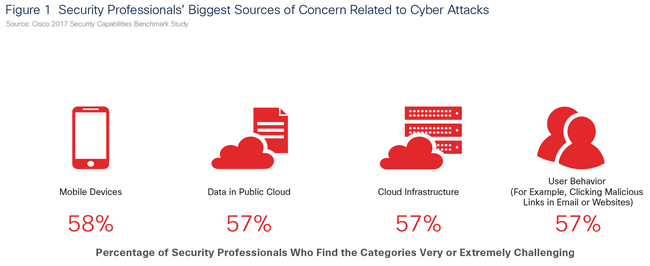
Executives of the companies who are responsible for informational security named lack of resources, incompatibility of informational security systems, and lack of qualified professionals among their most important barriers from promoting the main principles of informational security. The directors also added that 65% of organizations use from six to 50 or more systems of cybersecurity and this, as experts claim, contributes to development of new gaps in security.
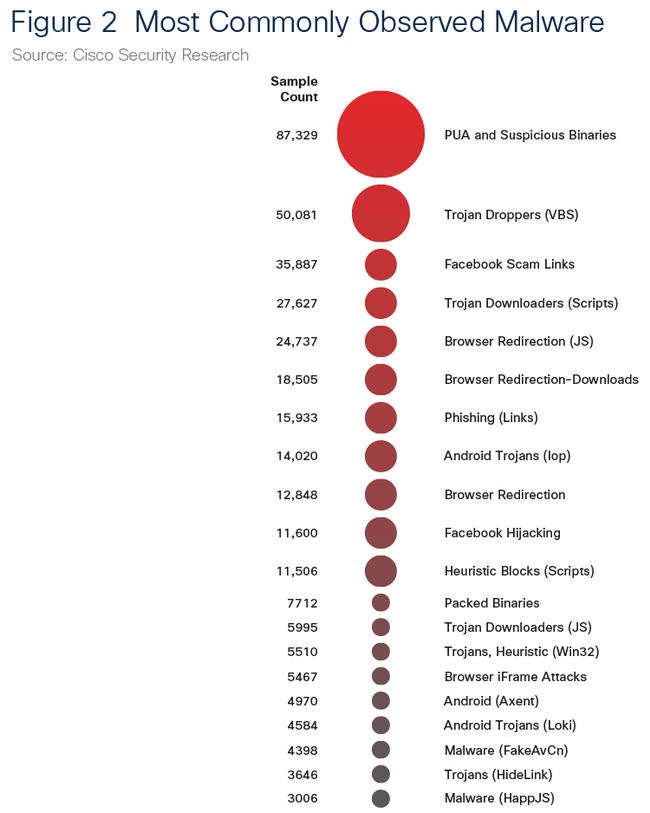
As the report claims, hackers use these gaps, returning to “past attacks” such as pilot versions of software and mail spam. It should be added that quantitative spam statistics amaze—almost two-thirds (65%) of messages are considered spam and 10% of them are regarded as dangerous. This already existed in 2010. In addition, more and more spam is being received from big botnets.
How much do cyber-threats cost for businesses: lost customers and small income
In its report, Cisco demonstrated the potential connection between cyberattacks and the company’s condition. Cyberattacks resulted in the following:
- 22% of organizations, which were attacked, have had the quantity of their clients reduced; moreover 40% of them have had the number of their customers decrease by 20%
- 29% had their income significantly reduced, 36% of them had their income decline by 20%
- 23% of affected companies have reported lost profit, 42% of them have lost more than 20% of beneficial offers
Cyber-attacks and new “business-models”
Last year is remembered for a new hackers’ tendency—cyber-groupings became more “corporate.”
Criminals use old, proven technical methods as before but together with that, they create new opportunities.
- New methods of hackers often look more and more like corporate hierarchy. Many organizations use so-called brokers or “floodgates” which work as middle management and mask malicious activity. All of this helps criminals because it allows them to accelerate their actions, take control over software space, and avoid detection.
- Usual adware, which “throws” advertisements without notifying users, shows its effectiveness again and again: more than 75% of studied organizations are infected by it.
- The great news was the reduced popularity of such large sets of exploits as Angler, Nuclear, and Neutrino, the activity of which was prevented in 2016 but smaller players quickly took their places.
How to minimize the risks of cyberattacks
For minimizing risks experts propose the following:
- The question of providing informational security should become one of business-priorities. Security has to become a daily question for executives.
- Research on operational disciplines. What should also be revised is existing security, adjustments of software, control over the access to networks, apps, functions, and data.
- Testing the effectiveness of the security.
- Systematic approach to the security. Integration and automation should be placed at the top of all security criteria. Systematic approach will let you better control and improve mutual compatibility and reduce the amount of time spent on detection and prevention of cyberattacks.
The development of technologies provokes the development of cyber-attacks’ methods but at the same time allows to protect from them more effectively. The most important part of this is the availability of a strong security base. Modern underground economy makes cybercrime a kind of business, which does not require many expenses. Nowadays criminals can be whoever they want and live wherever they want and they don’t need any extra knowledge. It is enough to purchase one of the exploits package.
As you can see from this article, the most important thing in prevention of cyber-attacks is paying enough attention to security and taking seriously any (even small) changes or malfunctions in the system in general or its particular parts.